Oracle® Identity and Access Manager / SOA Workflows OWSM default-keystore.jks
Regenerate the default-keystore.jks following the steps descrided in the document below :
1.In an empty working folder execute the following in order to generate a new keystore file:
keytool -genkey -alias xell -keyalg RSA -keysize 1024 -dname "CN=Customer, OU=Customer, O=Customer, L=City, ST=NY, C=US" -validity 3650 -keypass <password> -keystore default-keystore.jks -storepass <password> -storetype jks -provider sun.security.provider.Sun
Please ensure that JDK_HOME\jre\bin is in your PATH environment variable.
2.Generate a certifcate request:
keytool -certreq -alias xell -file xell.csr -keypass <password> -keystore default-keystore.jks -storepass <password> -storetype jks -provider sun.security.provider.Sun
3.Export the certificate:
keytool -export -alias xell -file xlserver.cert -keypass <password> -keystore default-keystore.jks -storepass <password> -storetype jks -provider sun.security.provider.Sun
4.Trust the certificate:
keytool -import -trustcacerts -alias xeltrusted -noprompt -keystore default-keystore.jks -file xlserver.cert -storepass <password>
5.Copy all the 3 generated files (default-keystore.jks, xell.csr, xlserver.cert) in MIDDLEWARE_HOME\user_projects\domains\<OIM Domain>\config\fmwconfig
You should repeat this step for each node in a clustered environment.
6.Change the values of the CSF keys for default-keystore.jks and xell:
- Login to Enterprise Manager
- Right-click the domain
- Navigate to Security, and then Credential
- Expand oim
- Edit default-keystore.jks and xell and change the password for both keys with the values used in steps 1-4.
Note: You should NOT change the passwords for other CSF keys!
7.Restart OIM server and check if everything is working fine.
One should do the following, saving in between :
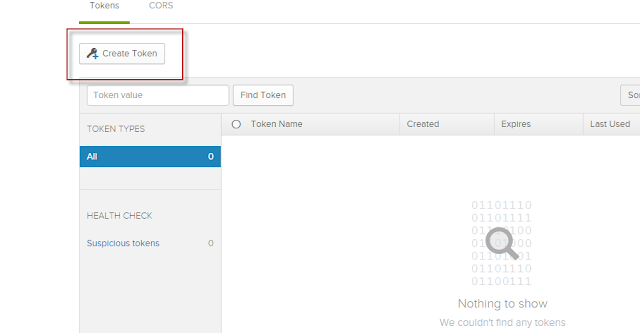
1) Go to EM --> --> Security --> Credentials
2) Expand oracle.wsm.security map
3) Change paswords of the following keys
- keystore-csf-key (user=owsm, password=keystore password)
- enc-csf-key (user=xell, password)
- sign-csf-key (user=xell, password)
- recipient-alias-key (user=xell, password)